In the last post, we looked at executing your first simulated attack by using the “Spear Fishing” attach that harvests credentials from a custom Office 365 login page.
For this post we will look at running a “Brute Force Password (Dictionary Attack)” as the simulated attack. Once again to start this, access the “Security and Compliance” center with your Office 365 Tenant, then expand “Threat Management” and choose “Attack simulator”.
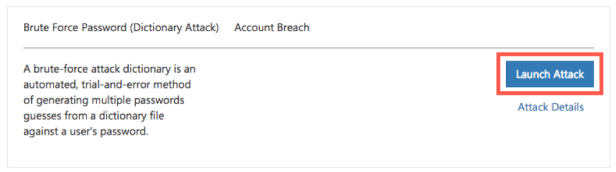
From the options, choose the attack “Brute Force Password” and press the “Launch Attack” button to begin the wizard.
Name the new campaign as “Brute Force Password Attack” and then press “Next”.

Select the target users, by choosing specific user accounts or groups.


Once you have selected the users or groups, press “Next” then set the password properties as needed.

Either a single password can be entered, which can be useful for checking single passwords. A file can also be uploaded, that contains multiple passwords, allowing for iteration of the password list against the selected accounts. You can download some password files from here:
https://github.com/danielmiessler/SecLists/tree/master/Passwords
Choose any of the password lists you want to use, download them and then choose file upload to add the file you need. This attack does not send an email to the end user, it simply tries to access the account, using the list of passwords that is supplied. Once the attack is complete, the status is updated, and a “View Report” link is then available.

Clicking this link then displays the number of accounts with passwords that matched any of the values within the password file used within the attack.

You can also see a short report by clicking the “Attack Details” link, within the specific attack displayed on the “Attack Simulator” page.

This attack is really for Security and IT to get the current state of passwords across the organization, allowing either training or new policies to be defined.
